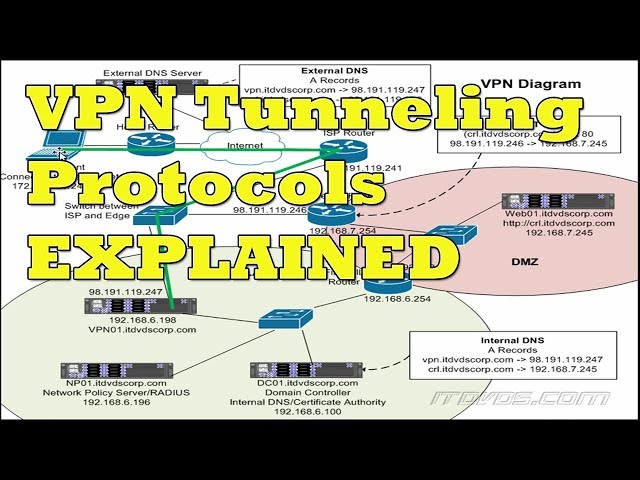
How Tunneling Is Accomplished in a VPN – Learn about the different methods used to create a VPN tunnel.
 Checkout this video:
Checkout this video:
Introduction
In computer networks, a tunneling protocol is a communications protocol that allows for the movement of data from one network to another. A tunnel is similar to a pipeline in that it is used to transport data from one location to another. The main difference between a tunnel and a pipeline is that a tunnel can be used to transport data across different types of networks, while a pipeline can only be used to transport data across similar types of networks.
Tunneling protocols are commonly used in Virtual Private Networks (VPNs) because they allow for the secure movement of data from one network to another. When data is sent through a tunnel, it is encrypted so that it cannot be read or tampered with by anyone who does not have the proper encryption key. This makes tunnels an important part of VPNs, which are often used by businesses to send sensitive data across the Internet without having to worry about it being intercepted or hacked.
There are many different types of tunneling protocols, and each has its own advantages and disadvantages. Some of the most popular tunneling protocols include:
-IPsec
-L2TP
-PPTP
-SSTP
-OpenVPN
What is a VPN?
A VPN, or Virtual Private Network, is a private network that extends across a public network or internet. When you connect to a VPN, you create a secure “tunnel” between your computer and the VPN server. All data passing through this tunnel is encrypted — meaning that anyone trying to intercept your data will not be able to read it. This is why VPNs are often used by businesses: it allows employees to securely connect to the company network from anywhere in the world, without the need for a physical connection.
There are two main types of VPNs: site-to-site and remote-access. A site-to-site VPN connects two locations (e.g., two office buildings in different cities) together so that devices at both locations can communicate as if they were on the same local network. A remote-access VPN allows individual users to securely connect to the network from anywhere in the world.
VPNs are accomplished by creating a “tunnel” between two devices. This tunnel is created by first encapsulating (or packaging up) all of the data traveling from one device to another in an extra layer of data known as a “tunneling protocol.” The most common tunneling protocols used for VPNs are IPsec, L2TP/IPSec, OpenVPN, PPTP, and SSTP.Once the data is encapsulated in the tunneling protocol, it is then encrypted using a second layer of security known as “encapsulation.” The most common encapsulation protocols used for VPNs are SSL/TLS and SSH.
After the data has been encapsulated and encrypted, it is then sent over the public network (or internet) to the VPN server. The VPN server decrypts the data and sends it on to its destination — which could be another computer on the same local network, or a website on the other side of the world. From start to finish, this process takes only a few milliseconds — making it impossible for anyone eavesdropping on your connection to read or tamper with your data.
What is Tunneling?
In computer networks, a tunneling protocol is a communications protocol that allows for the movement of data from one network to another. It involves establishing and maintaining a logical network connection (or “tunnel”) between two hosts. A tunneling protocol may be used to carry any kind of data.
One common use for tunneling is to allow a remote user to access a private network, such as a company’s internal network or a home LAN. The remote user connects to the tunneling server, which then forwards traffic to the desired destination. The most popular tunneling protocol is PPTP, which is used to connect to Microsoft VPN servers. Other common tunneling protocols include L2F, L2TP, and IPsec.
How Tunneling Is Accomplished in a VPN
When you connect to a VPN, all of your traffic is routed through a secure tunnel. This tunnel encrypts your data, making it unreadable to anyone who might intercept it. This is how a VPN protects your privacy and keeps your data safe.
The L2TP/IPSec Protocol
Layer 2 Tunneling Protocol (L2TP) is a combination of PPTP and Cisco’s Layer 2 Forwarding (L2F), a tunneling protocol originally developed by Cisco. L2TP encapsulates PPP frames and sends encapsulated data over any medium that supports point-to-point datagram delivery, such as IP or X.25. The encapsulation adds a layer of LC-header to the original frame.
L2F was primarily designed to support virtual private dialup networks (VPDNs). A VPDN is a user-to-LAN connection used to connect a remote user to the corporate network. L2F provides tunnel management and allows dialup users to access private resources, such as email servers, file servers, and print servers, as if they were on the corporate network. L2F can also be used over the Internet to connect two private networks.
Cisco combined L2F with PPTP and extended it to work over any type of medium, such as IP, ATM, Frame Relay, or X.25. L2TP uses UDP port 1701 and is supported by many vendors, including Microsoft in Windows 2000 Server and Windows Server 2003.
Like PPTP, L2TP requires that the VPN server have an IP address that is reachable from the VPN client’s location; however, it does not require that the VPN server have a public-facing DNS name or be located on the Internet.
The PPTP Protocol
The Point-to-Point Tunneling Protocol (PPTP) is a method for implementing VPNs. PPTP uses a control channel over an IP network, and a GRE tunnel operating to encapsulate PPP packets. The benefit of PPTP is that it can be implemented without modifying network routers.
A big advantage of PPTP is that it uses the Generic Routing Encapsulation (GRE) protocol to encapsulate data. GRE is supported by most devices that also support IP, which makes it relatively easy to implement PPTP. However, GRE does have some security issues that need to be considered.
When using PPTP, data is encrypted using the Microsoft Point-to-Point Encryption (MPPE) protocol. MPPE uses the RC4 stream cipher with a 128-bit key. MPPE is generally considered to be secure, but there have been some troubling reports about its security in recent years.
The SSL/TLS Protocol
The SSL/TLS protocol is the most common method for accomplishing VPN tunneling. This protocol uses a combination of public key cryptography and symmetric key cryptography to encrypt data as it travels across the Internet. Data that is encrypted with the public key can only be decrypted with the private key, and vice versa. This ensures that only the intended recipient of the data can read it.
The OpenVPN Protocol
OpenVPN is an open-source VPN protocol allowing secure point-to-point connections in routed or bridged configurations. It uses a custom security protocol that utilizes SSL/TLS for key exchange. It is capable of traversing network address translators (NATs) and firewalls. It was written by James Yonan and is published under the GNU General Public License (GPL).
OpenVPN supports bidirectional authentication based on certificates, password-based authentication, and two-factor authentication using Google Authenticator. A single OpenVPN server can support multiple simultaneous client connections, and a single client connection can be routed through multiple OpenVPN servers. OpenVPN has been ported to multiple platforms, including Linux, FreeBSD, OpenBSD, NetBSD, Mac OS X, Solaris, Cisco Routers and Android.
Conclusion
To conclude, tunneling is a process of encapsulating data within an IP datagram. This enables the sending of data that would normally be blocked by security devices, such as firewalls. Tunneling can be used to add security to an existing connection, or to create a new, secure connection where none existed before.
